I think there are two main reasons why Windows would wake up “by itself” (without pressing a key on the keyboard or clicking the mouse).
- Scheduled tasks;
- Devices allowed to wake up the computer.
Scheduled tasks are fairly simple to look into and it was not the problem at the time of writing this post, so I’ll skip straight to the second point.
We can get a list of devices that are allowed to wake up the computer from sleep by typing at the command prompt:
powercfg -devicequery wake_armed
At the time, I had 3 allowed devices:
- Intel(R) 82579V Gigabit Network Connection
- HID-compliant mouse
- Microsoft USB Natural Ergonomic Keyboard 4000 (Mouse and Keyboard Center) (001)
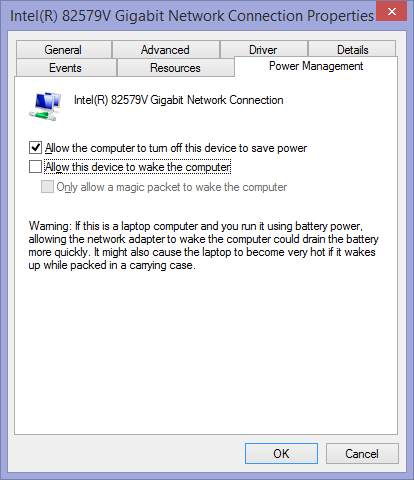
I don’t need WOL or anything like that so I disallowed the network card to wake up the computer using Device manager:
And voilà, my computer now stays asleep until I use the mouse or keyboard. I started having this problem after moving the computer to another network, so I suspect the new router or other network connected computers sent packets that waked it up.